My API is called JMemPGP (Java Memory PGP). The only files it needs are public and private keys, depending on what operation you want. The actual input and output data consist of a pair of byte[] arrays. If you want to use a String, you can use the String.getBytes() method.
I'm going to demonstrate the 4 basic PGP operations using JMemPGP: encrypt, decrypt, sign, and verify.
For this tutorial, you need GPG4Win, GPGshell, NetBeans, and two files from the Bouncy Castle website. Start NetBeans downloading now. Make sure to get a version that contains the JDK.
First, download and install GPG4Win and GPGshell. Then open Kleopatra and create a certificate. If you're not prompted to create one at startup, then navigate to File->New Certificate...
Click "Create a personal OpenPGP key pair", fill in the fields on the next page, and then I would suggest going into "Advanced Settings" and changing the key size to 4096, but that's not necessary to continue. Click Next and then Create Key. Follow the instructions shown for providing random input. When you're done, you should see your new certificate in the list.
Right-click it and choose "Export Certificates..."
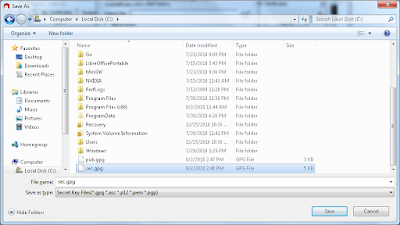
Let's save it to the C drive. You might have to save it to a different folder if you're on Windows 10. Let's name it pub.gpg.
Now right-click the certificate again and choose "Export Secret Keys..." Make sure "ASCII armor" is unchecked. Save it as sec.gpg and click OK.
You should now have two files, as shown:
Now we need those two files from the Bouncy Castle website. Navigate to https://www.bouncycastle.org/latest_releases.html and scroll down to the "Signed Jar Files" section.
You need the two files that are highlighted. There may be a newer version by the time you download it and that's fine.
Now it's time to install NetBeans. The installer is pretty simple so just run it. Once it's done, open NetBeans and navigate to File->New Project...
The default project type should be a Java Application, so click Next. For a project name, just type PGPTutorial.
Now right-click the project's package in the pane on the left and choose New->Java Class...
Call the new class JMemPGP and click Finish. Now we need to install the Bouncy Castle API. Right-click the project this time, the item at the top with capital letters, and choose Properties at the bottom of the menu. Now choose the Libraries category and click "Add JAR/Folder".
Use the Ctrl key to select both JAR files, click Open, and then click OK to exit the Properties dialog.
Now visit my article on yours.org to get the JMemPGP API. It costs $1 to unlock the paywall. Once you're in, select the code and copy it to the clipboard. In NetBeans, go to your file JMemPGP.java, which should be open in the editor already, and replace the contents with what you just copied, but make sure to preserve the line "package pgptutorial;". Now click the Save All button at the top or press Ctrl+S.
There are just a couple more things we need. Add the following imports to your main file, PGPTutorial.java.
import java.io.ByteArrayInputStream;
import java.io.ByteArrayOutputStream;
import java.security.Security;
import org.bouncycastle.jce.provider.BouncyCastleProvider;
Change your main() method to:
public static void main(String[] args) throws Exception{
Finally, add this line to the beginning of your main() method:
Security.addProvider(new BouncyCastleProvider());
Now we're ready to start using the API for the 4 basic PGP operations. Here is what PGPTutorial.java should look like when you're done.
The 4 basic PGP operations
Encrypt
Let's say we want to encrypt the string "OneDirection" with our PGP public key. Copy this code to update your main() method:
This code starts with a String, converts it to a byte[] array, connects a ByteArrayInputStream to the byte[] array, encrypts the data, and returns it in a ByteArrayOutputStream. This is converted back to a byte[] array, and then to a String for printing to the screen.
Run the app and you should get output similar to this:
You can copy-paste the PGP message block and decrypt it with GPGtray. You could paste it into GPGtray's text window and decrypt from there, but we'll just use the quick decrypt option. Right-click the tray icon and select "Clipboard Decrypt.../Verify".
You should be prompted for the passphrase you used when you created your certificate. Enter it and click OK. Here is what your output should look like.
Notice that it says "0/12 Bytes". This means that our program encrypted just the 12 bytes in "OneDirection", with no padding.
You can also encrypt custom byte arrays, such as binary data.
Again, notice that we get an output of precisely 5 bytes.
This code starts with a String, converts it to a byte[] array, connects a ByteArrayInputStream to the byte[] array, encrypts the data, and returns it in a ByteArrayOutputStream. This is converted back to a byte[] array, and then to a String for printing to the screen.
Run the app and you should get output similar to this:
You can copy-paste the PGP message block and decrypt it with GPGtray. You could paste it into GPGtray's text window and decrypt from there, but we'll just use the quick decrypt option. Right-click the tray icon and select "Clipboard Decrypt.../Verify".
You should be prompted for the passphrase you used when you created your certificate. Enter it and click OK. Here is what your output should look like.
Notice that it says "0/12 Bytes". This means that our program encrypted just the 12 bytes in "OneDirection", with no padding.
You can also encrypt custom byte arrays, such as binary data.
Again, notice that we get an output of precisely 5 bytes.
Decrypt
We can also decrypt from within Java. Notice that this time we have to provide our passphrase within the program. I used "test" as mine.
Output should be similar to this:
The output will be a detached signature. If you were to type the text "OneDirection" into Notepad and save it as a *.txt file, you could copy-paste this detached signature into a file and save it as *.txt.asc and verify it with GpgEx.
Now right-click file.txt.asc and choose More GpgEx options->Verify.
Click "Decrypt/Verify".
As you would expect, if you change file.txt at all, the signature will not work. Let's change the text to "OneRepublic" and see what happens.
Save file.txt and try verifying it again.
Now right-click file.txt.asc and choose More GpgEx options->Verify.
Click "Decrypt/Verify".
As you would expect, if you change file.txt at all, the signature will not work. Let's change the text to "OneRepublic" and see what happens.
Save file.txt and try verifying it again.
Verify
You can also verify signatures from within Java.
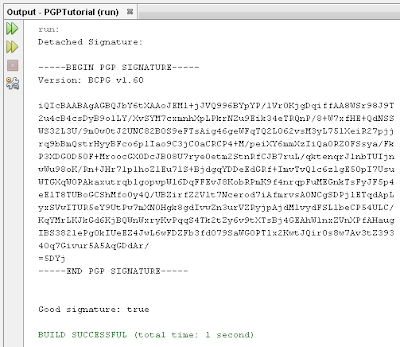
Copy and paste this code, run it, and look at the last line it prints.
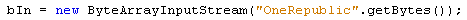
Let's change the line that says
bIn = new ByteArrayInputStream(str);
to say
bIn = new ByteArrayInputStream("OneDirection".getBytes());
Run the program again and you'll see that the signature is still valid. But if you change the string to say "OneRepublic" like in the last example, the signature will not match.
Run the program again and see what the last line says.
Let's change the line that says
bIn = new ByteArrayInputStream(str);
to say
bIn = new ByteArrayInputStream("OneDirection".getBytes());
Run the program again and you'll see that the signature is still valid. But if you change the string to say "OneRepublic" like in the last example, the signature will not match.
Run the program again and see what the last line says.






















I would buy your API code, but asking a newbie to set up a Bitcoin SV wallet, buy coins to put into that wallet, then link that wallet to an on-line wallet service, in order to push $1 to you, is too big of an ask.
ReplyDeleteI didn't have PayPal when I wrote this. I don't want to share my email address here but if you contact me on Discord (@DoaJC_Blogger#1621) I'll provide a PayPal email you can send $1 to.
Delete