Right now, the transmit function seems to only work on Linux. I tried on Windows and got varying results. Initially I was able to transmit some distorted FM audio in the Windows version of GNUradio, but I could not transmit a digital QPSK signal. It's been a while since I tried, but I don't think I can transmit anything in Windows anymore. Currently, when I try to transmit from Windows, I get an unstable solid carrier.
On the LostCarrier.Online Discord channel, Ballistic Autistic told everyone that he succeeded in transmitting good FM audio with his LimeSDR Mini from GNUradio on Ubuntu. I asked him if he would try QPSK and send me a reception screenshot, which he did.
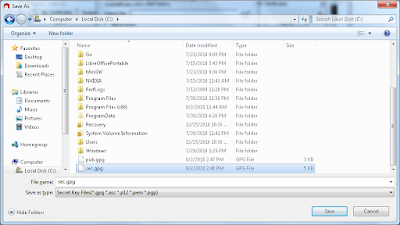
Credit: Ballistic Autistic
Once I knew that it was possible to make it work, I downloaded the GNUradio Live DVD image, which is a Ubuntu distribution, and used Universal USB Installer to install it to a flash drive. I installed the driver, compiled and installed gr-limesdr, and then had a working transmit setup. Since it's hard to find instructions for using the LimeSDR Mini, I'll explain the full process.
I would recommend updating the firmware on your LimeSDR Mini, but I don't think it's necessary if you don't want to.
I would recommend updating the firmware on your LimeSDR Mini, but I don't think it's necessary if you don't want to.
Transmitting with a LimeSDR Mini, start to finish
1. Download the GNUradio Live DVD image. Get it from here: GNU Radio Live SDR Environment
2. Install it to a flash drive using Universal USB Installer. I chose to have a 1GB persistent area.
3. Boot from the drive
4. Open a terminal (command prompt) and enter the commands linked here to install the driver in Ubuntu.
5. Run "mkdir gr-limesdr"
6. Visit https://github.com/myriadrf/gr-limesdr and enter the commands shown for Linux installation.
7. Open GNUradio Companion. You should now have LimeSDR source and sink blocks. You can click in the list of blocks on the right and press Ctrl+F to search for them.
If you haven't already, plug in your LimeSDR Mini. Now let's put together a flowgraph to test the transmitting function. You should have a second SDR on another computer to receive with.
Transmitting FM audio
Before starting, make sure you have a WAV file recorded as 48 kHz mono.
In GNUradio Companion, click Open and you should see a "ubuntu" folder on the left. Navigate there if it's not already selected and then open gr-limesdr/examples/FM_transmitter.grc.
1. Remove the "LimeSuite Sink (TX)" block, and add a fresh one from the list on the right.
2. Connect the output of "Rational Resampler" to the input of the new "LimeSuite Sink (TX)" block.
3. Double-click the LimeSuite block and you'll see that the "Device serial" field is empty. Make sure your LimeSDR Mini is connected with USB, then open a terminal and run "LimeUtil --find". This will print a list of all Lime devices. Copy the serial number of yours and paste it into the LimeSuite block's "Device serial" field.
4. Change "Device type" to LimeSDR-Mini
5. Choose an "RF frequency" that you want to transmit on. Even though there is very little transmit power, you want to choose a frequency that won't interfere with anything. I like 903.4 MHz but that's not usually license-free outside North America. Frequencies are measured in Hz, so you could type something like 903400000 or just 903.4e6, with e6 meaning MHz.
6. Set the "Sample rate" to 5e6, which means 5 MHz. Click OK.
7. Double-click the "Rational Resampler" block. Change "Interpolation" to 125 and "Decimation" to 12. Click OK.
The Resampler converts the 480 kHz FM quadrature (a.k.a. IQ data; in the next step) to 5 MHz. This block converts between IQ sample rates using the formula
output_rate = input_rate * (Interpolation/Decimation).
Since the FM block will output IQ data at a rate of 480 kHz and we're transmitting with 5 MHz bandwidth,
480000 * (125/12) = 5000000
8. Double-click the "NBFM Transmit" block. Change "Audio Rate" to 48000. Change "Quadrature Rate" to 480000. Change "Max Deviation" to your desired FM deviation. I'm going to use 24e3 (24 kHz). Click OK.
9. Finally, double-click the "Wav File Source" block. For the "File" field, click the "..." button to browse for the WAV file you want to transmit. Once it's in the "File" field, click OK.
Connect a receive SDR to another computer, open your desired SDR program, and navigate to the frequency you chose. At the computer you'll be transmitting with, connect your LimeSDR Mini to an antenna and click the green play button at the top. The result should be clear FM audio.
For some reason, I can't get my SDR to transmit on low frequencies like FM broadcast or the 6m ham band. Frequencies like 400 MHz and higher work well, but 900 MHz seems to work best.
1. Create a new flowgraph and follow the instructions in the previous example to set up a "LimeSuite Sink (TX)" block. For this section I set mine, on the CH0 tab, to use a digital filter of about 750 kHz. This makes the signal edges look cleaner in the waterfall.
2. Add the following blocks: "Constellation Modulator" and "Constellation Object".
3. Double-click the "Constellation Modulator" block. In "Constellation", point it to the "Constellation Object" block by entering its name, variable_constellation_0. Change "Differential Encoding" to No and "Samples/Symbol" to 8. Click OK.
We're going to try transmitting a "Random Source" with random values evenly distributed between 0 and 255, and optionally a file with non-random data.
4. Add a "Random Source" block and double-click it. Change "Output Type" to Byte, "Minimum" to 0, and "Maximum" to 255. Click OK.
5. Connect the output of "Random Source" to the input of "Constellation Modulator". Connect the output of "Constellation Modulator" to the input of "LimeSuite Sink (TX)".
6. (Optional) Now add a "File Source" block and double-click it. Change "Output Type" to Byte. Choose a file and click OK. Right-click the block and choose Disable, then connect its output to the input of "Constellation Modulator".
Click the green play button to run the flowgraph.
For my optional file, I chose the Monero blockchain. Notice that the signal is not as smooth because the file isn't very random. If you want to switch between Random Source and File Source, just disable one and enable the other.
1. Follow the instructions above to create the flowgraph but don't transmit yet.
2. Double-click the "Constellation Object" block and change "Constellation Type" to 16QAM. Click OK and then try transmitting.
You'll notice that 16-QAM produces a smoother signal than QPSK.
Like the previous section, the random source transmission power had to be reduced by 5 dB so the waterfalls would look the same.
In GNUradio Companion, click Open and you should see a "ubuntu" folder on the left. Navigate there if it's not already selected and then open gr-limesdr/examples/FM_transmitter.grc.
1. Remove the "LimeSuite Sink (TX)" block, and add a fresh one from the list on the right.
2. Connect the output of "Rational Resampler" to the input of the new "LimeSuite Sink (TX)" block.
3. Double-click the LimeSuite block and you'll see that the "Device serial" field is empty. Make sure your LimeSDR Mini is connected with USB, then open a terminal and run "LimeUtil --find". This will print a list of all Lime devices. Copy the serial number of yours and paste it into the LimeSuite block's "Device serial" field.
4. Change "Device type" to LimeSDR-Mini
5. Choose an "RF frequency" that you want to transmit on. Even though there is very little transmit power, you want to choose a frequency that won't interfere with anything. I like 903.4 MHz but that's not usually license-free outside North America. Frequencies are measured in Hz, so you could type something like 903400000 or just 903.4e6, with e6 meaning MHz.
6. Set the "Sample rate" to 5e6, which means 5 MHz. Click OK.
7. Double-click the "Rational Resampler" block. Change "Interpolation" to 125 and "Decimation" to 12. Click OK.
The Resampler converts the 480 kHz FM quadrature (a.k.a. IQ data; in the next step) to 5 MHz. This block converts between IQ sample rates using the formula
output_rate = input_rate * (Interpolation/Decimation).
Since the FM block will output IQ data at a rate of 480 kHz and we're transmitting with 5 MHz bandwidth,
480000 * (125/12) = 5000000
8. Double-click the "NBFM Transmit" block. Change "Audio Rate" to 48000. Change "Quadrature Rate" to 480000. Change "Max Deviation" to your desired FM deviation. I'm going to use 24e3 (24 kHz). Click OK.
9. Finally, double-click the "Wav File Source" block. For the "File" field, click the "..." button to browse for the WAV file you want to transmit. Once it's in the "File" field, click OK.
Connect a receive SDR to another computer, open your desired SDR program, and navigate to the frequency you chose. At the computer you'll be transmitting with, connect your LimeSDR Mini to an antenna and click the green play button at the top. The result should be clear FM audio.
For some reason, I can't get my SDR to transmit on low frequencies like FM broadcast or the 6m ham band. Frequencies like 400 MHz and higher work well, but 900 MHz seems to work best.
The resulting signal received with an SDRplay RSP1
Transmitting QPSK
For this experiment, I'm going to transmit a QPSK signal with a rate of 1.25 Mbit/sec.1. Create a new flowgraph and follow the instructions in the previous example to set up a "LimeSuite Sink (TX)" block. For this section I set mine, on the CH0 tab, to use a digital filter of about 750 kHz. This makes the signal edges look cleaner in the waterfall.
2. Add the following blocks: "Constellation Modulator" and "Constellation Object".
3. Double-click the "Constellation Modulator" block. In "Constellation", point it to the "Constellation Object" block by entering its name, variable_constellation_0. Change "Differential Encoding" to No and "Samples/Symbol" to 8. Click OK.
We're going to try transmitting a "Random Source" with random values evenly distributed between 0 and 255, and optionally a file with non-random data.
4. Add a "Random Source" block and double-click it. Change "Output Type" to Byte, "Minimum" to 0, and "Maximum" to 255. Click OK.
5. Connect the output of "Random Source" to the input of "Constellation Modulator". Connect the output of "Constellation Modulator" to the input of "LimeSuite Sink (TX)".
6. (Optional) Now add a "File Source" block and double-click it. Change "Output Type" to Byte. Choose a file and click OK. Right-click the block and choose Disable, then connect its output to the input of "Constellation Modulator".
Click the green play button to run the flowgraph.
For my optional file, I chose the Monero blockchain. Notice that the signal is not as smooth because the file isn't very random. If you want to switch between Random Source and File Source, just disable one and enable the other.
Random bytes from 0 to 255 inclusive
Monero blockchain
I had to reduce the transmit power by 5 dB for the random source because it appears to produce a much stronger signal.
Transmitting 16-QAM
This experiment will produce a 16-QAM signal with a rate of 2.5 Mbit/sec. It will occupy the same RF bandwidth as the QPSK signal in the previous section.1. Follow the instructions above to create the flowgraph but don't transmit yet.
2. Double-click the "Constellation Object" block and change "Constellation Type" to 16QAM. Click OK and then try transmitting.
You'll notice that 16-QAM produces a smoother signal than QPSK.
Random bytes from 0 to 255 inclusive
Monero blockchain
Like the previous section, the random source transmission power had to be reduced by 5 dB so the waterfalls would look the same.